as the demand for cross-border business and access to mainland china grows, the us cn2 high-defense vps has become the first choice of many webmasters and enterprises. cn2 lines provide better mainland backhaul quality, and high-defense vps additionally integrates ddos cleaning capabilities to ensure business continuity during attacks. it is an important direction for server, vps and host deployment.
at the network architecture level, a mature us cn2 high-defense vps solution should include: multi-line bgp access (prioritizing cn2 gt/backbone), deployment of high-performance forwarding equipment and routing strategies, and redundant links with upstream operators and cleaning centers to form multi-path backup and reduce the risk of single point failure.
the best practice for traffic scheduling is firstly policy-based routing (pbr) and bgp flexible routing, combined with anycast and intelligent dns to achieve traffic balancing. for external services, it is recommended to use low-ttl dns health check and cooperate with dynamic scheduling. when some nodes are attacked, they can quickly switch to backup nodes or cdn back to the origin.
in terms of ddos protection, high-defense vps should support traffic cleaning, rate limiting, protocol anomaly detection and status synchronization. computer rooms carrying cn2 lines can usually provide backup cleaning centers. combining black hole routing and hierarchical cleaning can maintain core business availability during peak attack periods while minimizing the inadvertent killing of normal traffic.
combining with cdn is a common solution to improve attack resistance and accelerate access. static resources are distributed through global cdn nodes, and edge caching and back-to-source current limiting are used to reduce vps pressure; dynamic requests are optimized through intelligent scheduling and connection pools to optimize back-to-source links to improve concurrent processing capabilities and reduce delays.
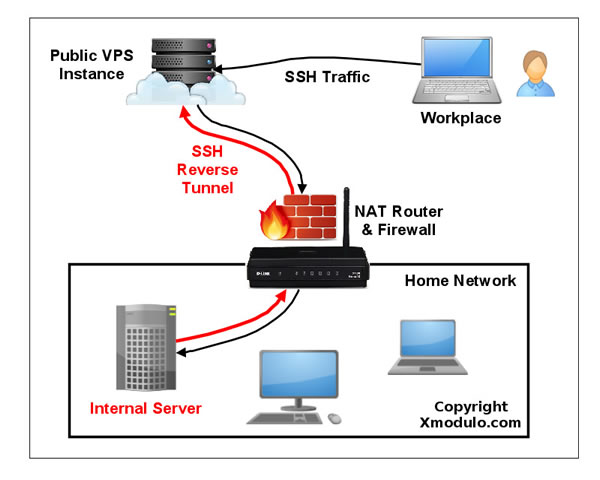
in specific implementation, it is recommended to adopt load balancing (l4/l7) and reverse proxy architecture, and use automatic expansion and health check for back-end services. combined with connection tracking, syn cookie and tcp concurrency control, it can effectively mitigate common state exhaustion attacks and ensure application layer stability.
operation and maintenance monitoring and alarming are an important part of the traffic scheduling closed loop. through real-time traffic analysis, anomaly detection and traffic playback tools, attack trends can be identified in advance and acls, black and white lists or trigger cleaning strategies can be adjusted. traffic logs are retained for subsequent traceability and auditing.
at the domain name and resolution level, proper configuration of dns hosting, backup ns, and use of intelligent resolution services can enable rapid switching when a node fails or suffers a regional attack. it is recommended to link domain name resolution with cdn/load balancing and set health check and automatic recovery strategies.
purchasing and selection suggestions: prioritize us computer rooms that support cn2 high-quality backhaul, confirm high-defense bandwidth and peak-based billing/cleaning volume billing strategies, and check sla and attack and defense capability test records. for e-commerce, gaming and financial businesses, you can purchase packages with application firewall (waf) and professional operation and maintenance support, and conduct traffic drills when necessary.
if you are looking for a stable us cn2 high-defense vps service, it is recommended to consider dexun telecommunications. dexun telecom provides cn2 optimized lines, professional ddos cleaning, global cdn acceleration and 24/7 technical support. the packages are diverse and support on-demand expansion. it is suitable for sites and enterprises with high requirements for connection quality and security. welcome to visit dexun telecom to learn more and place an order.
- Latest articles
- Compliance Verification Korean Native Ip Query Url Application Scenarios And Examples In Corporate Risk Control
- Alternative Server Recommendation And Delay Comparison After Jian Wang 3 Closes The Vietnam Server
- How Enterprise-level Applications Improve Request Stability Through Taiwan's Proxy Server Cloud Host
- Selection Recommendations: The Best Cost-effective Configuration Within The Price Range Of Korean High-defense Servers
- Experts Share Tips On Shopee Store Clusters In Taiwan, Including Key Points In Customer Service Operations And Logistics Optimization
- Analysis Of Which Cloud Server In Malaysia Is Better From A Developer’s Perspective, Evaluation Of Ease Of Deployment And Interface Friendliness
- What Does Japanese Native Ip Mean? Its Practical Application Scenarios In E-commerce Operations
- From The Perspective Of Compliance And Audit, Look At What Hong Kong High-defense Servers Do To Meet Data And Operational Specifications
- Comprehensive Analysis Of Malaysia Vps Server Room Location And Delay Impact
- Stress Testing, Monitoring Strategies And Sla Inspection Indicators Before Renting A Korean Server Group
- Popular tags
-
Security Analysis Of Cn2 Server In Los Angeles, Usa
this article analyzes the security of the high-defense los angeles cn2 server and discusses its characteristics and advantages. -
Understanding The Factors Affecting The Speed Of Us Cn2 From International Links To Local Backbones
an in-depth analysis of "is the us cn2 fast?": from <b>international links</b> , <b>submarine optical cables</b> , <b>bgp routing</b> to local backbones and access, every link will tell you how to test, judge and optimize cross-border network performance. -
Benefits And Precautions For Using The Us Cn2 Server
this article deeply discusses the benefits of using the us cn2 server and related precautions to help users choose the appropriate server.